东西向流量控制
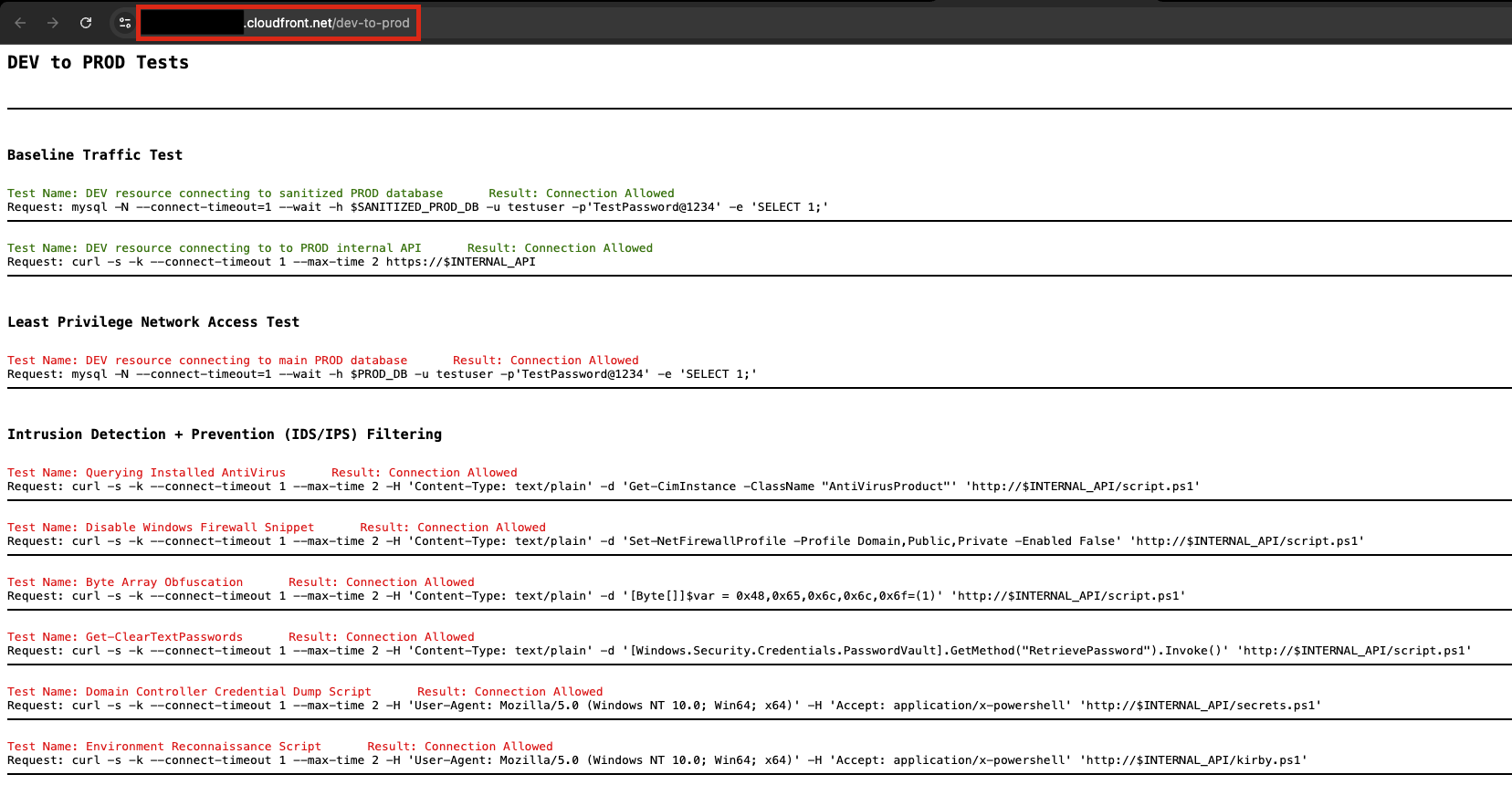
测试当前 DEV-to-PROD 流量
打开一个新的浏览器标签页并导航到 DEV-to-PROD 测试器脚本 URL,URL 格式为:
https://<CloudFront-Distribution-Domain>/dev-to-prod
在本实验中,我们将使用 AWS Network Firewall 来保护我们的开发和生产 VPC 之间的东西向流量。Network Firewall 提供有状态检测,使我们能够防止横向移动并在隔离环境中遏制潜在的安全漏洞。传统的边界安全侧重于南北向流量(往返互联网),但突破边界的攻击者通常会在内部系统之间横向移动。
配置 VPC 之间的最小权限访问
在 VPC 之间实施最小权限访问,确保只允许明确要求的流量流动,而所有其他通信默认被阻止。这可以防止未经授权的横向移动,并在某个环境遭到入侵时限制影响范围。在本节中,我们将使用 Suricata flowbits 创建一种允许列表方法,将特定连接标记为允许,其他所有连接均被拒绝。
配置有状态规则以实现最小权限访问
- 导航至 VPC → Network Firewall → Firewall policies
- 选择 egress-and-east-west-firewall-policy
- 向下滚动并选择 StatefulRuleGroup
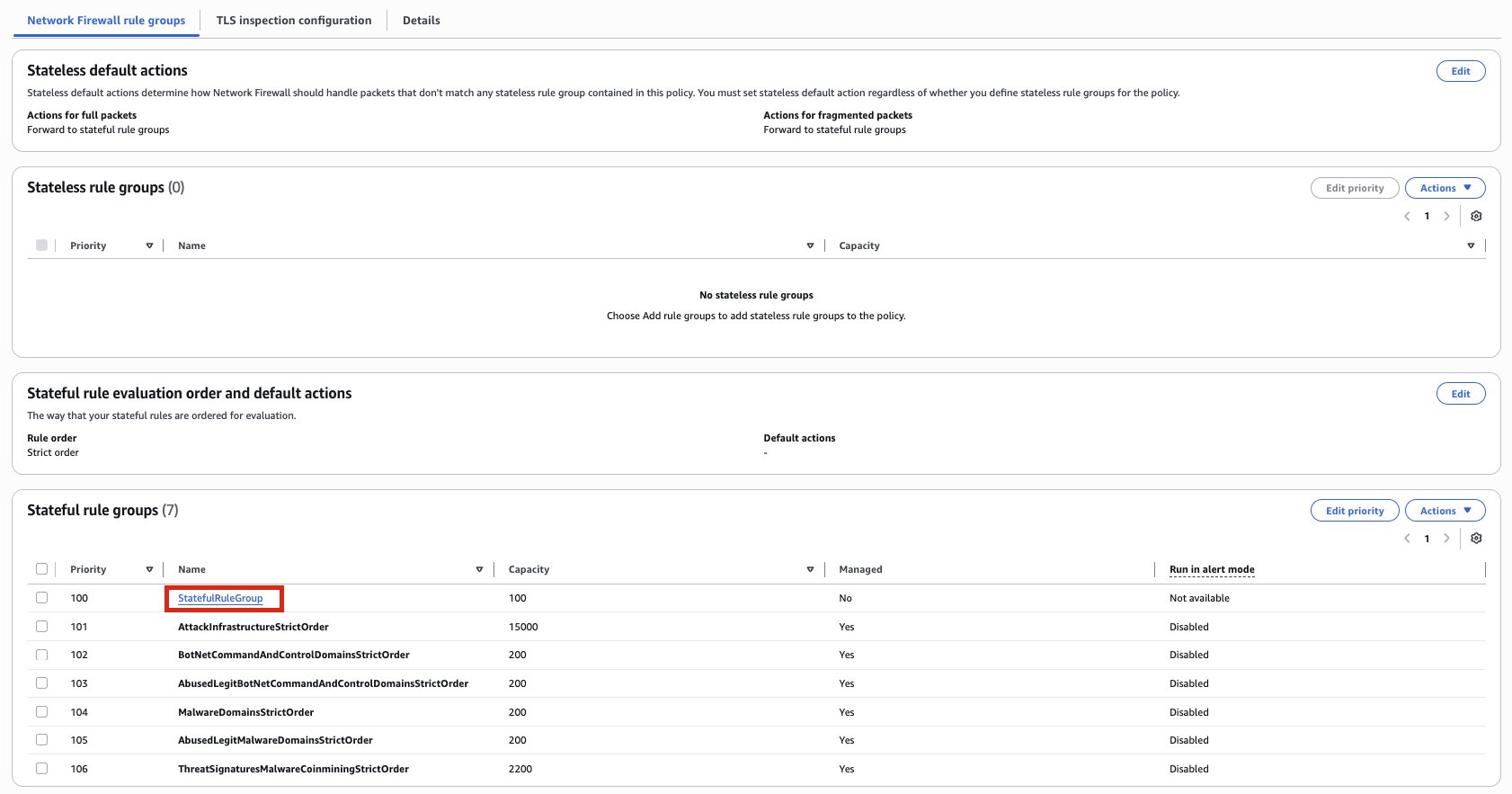
- 在规则下,选择 Edit
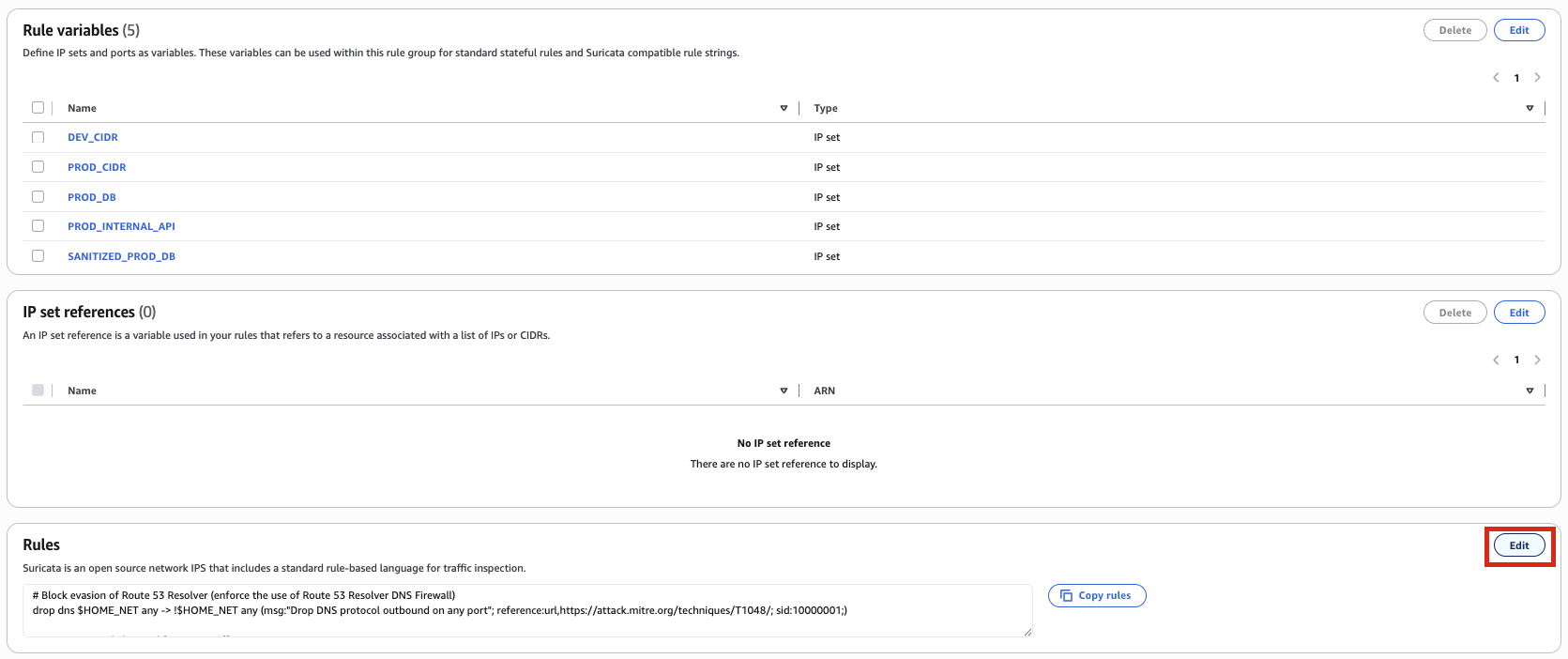
- 在规则集的顶部添加以下规则,位于上一个出口部分的规则之上:
# Allow TCP 3-way handshake
pass tcp any any -> any any (flow:to_server,not_established; sid:10001;)
# Mark MySQL connection from DEV to PROD sanitized database as allowed
alert tcp $DEV_CIDR any -> $SANITIZED_PROD_DB 3306 (msg:"Allow DEV to PROD sanitized DB"; flowbits:set,allow; flow:to_server; sid:10002;)
# Mark TLS connection from DEV to PROD internal API as allowed
alert tls $DEV_CIDR any -> $PROD_INTERNAL_API 443 (msg:"Allow DEV to PROD internal API over TLS"; flowbits:set,allow; flow:to_server; sid:10003;)
# Mark HTTP connection from DEV to PROD internal API as allowed
alert http $DEV_CIDR any -> $PROD_INTERNAL_API 80 (msg:"Allow DEV to PROD internal API over HTTP"; flowbits:set,allow; flow:to_server; sid:10004;)
# Reject any other TCP connections from DEV to PROD (Send a TCP reset so it's clear the connection was blocked by firewall and not a routing issue)
reject tcp $DEV_CIDR any -> $PROD_CIDR any (msg:"UNAUTHORIZED DEV -> PROD TCP CONNECTION ATTEMPT"; flowbits:isnotset,allow; flow:to_server; sid:10005;)
# Drop any other IP connections from DEV to PROD (Catch all drop rule for non TCP based protocols)
drop ip $DEV_CIDR any -> $PROD_CIDR any (msg:"UNAUTHORIZED DEV -> PROD NON-TCP CONNECTION ATTEMPT"; flowbits:isnotset,allow; flow:to_server; ip_proto: !TCP; sid:10006;)
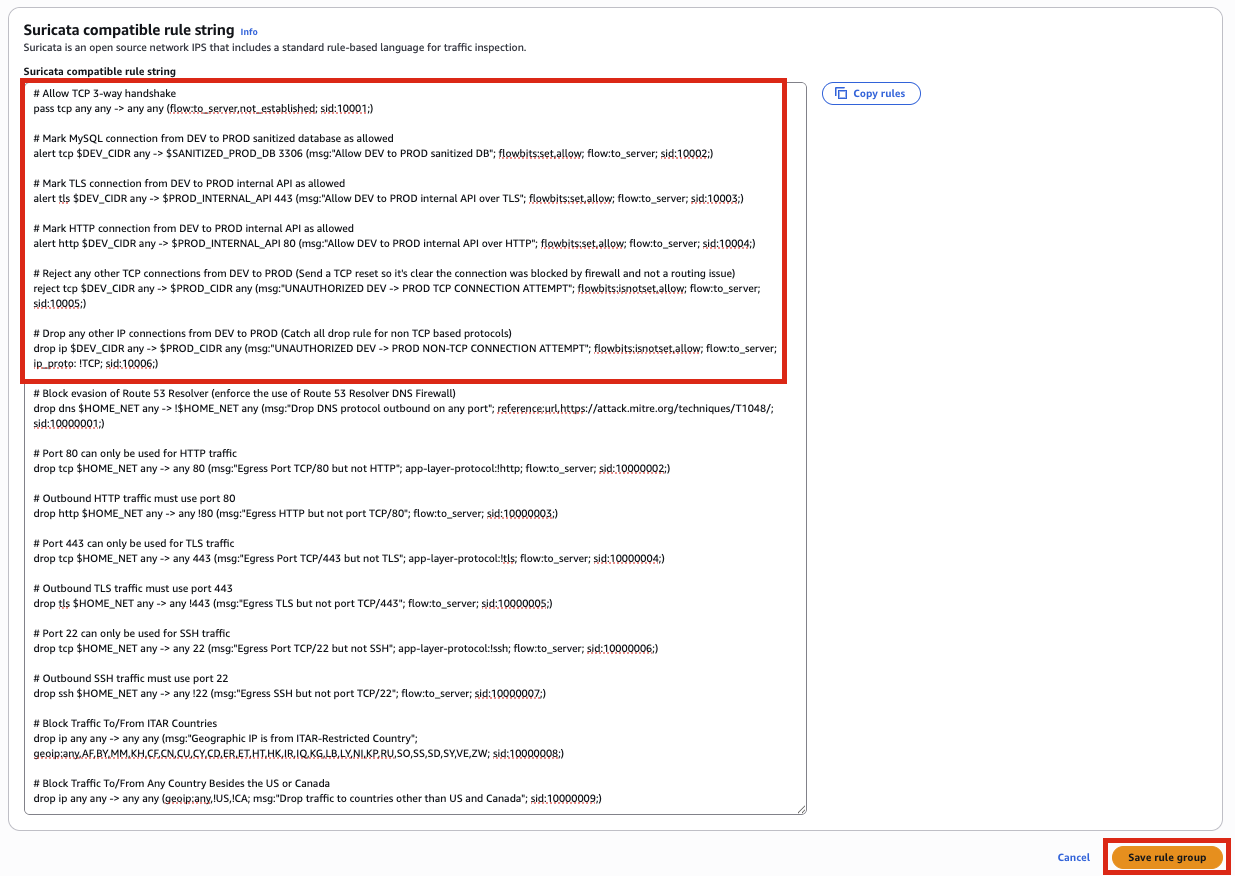
- 点击 Save
有关这些防火墙规则的说明, 整体逻辑如下:
DEV 环境 ──► PROD 环境
只允许:
├── 访问脱敏数据库 (MySQL 3306)
├── 访问内部 API (HTTPS 443)
└── 访问内部 API (HTTP 80)
其他全部拒绝
# Allow TCP 3-way handshake
pass tcp any any -> any any (flow:to_server,not_established; sid:10001;)
- 此规则允许从任意源到任意目标的初始 TCP 握手(SYN 数据包)。
flow:to_server,not_established关键字确保此规则仅匹配发往服务器且不属于已建立连接的流量。这是在应用更具体的规则之前允许发起新 TCP 连接所必需的。
# Mark MySQL connection from DEV to PROD sanitized database as allowed
alert tcp $DEV_CIDR any -> $SANITIZED_PROD_DB 3306 (msg:"Allow DEV to PROD sanitized DB"; flowbits:set,allow; flow:to_server; sid:10002;)
- 此规则识别并标记从开发环境到已清理的生产数据库的 MySQL 流量(端口 3306)为允许状态。
flowbits:set,allow关键字在此连接上设置名为 “allow” 的标志,后续规则将检查此标志。此规则使用alert动作,这意味着它将记录连接,但仍允许其被其他规则评估。
# Mark TLS connection from DEV to PROD internal API as allowed
alert tls $DEV_CIDR any -> $PROD_INTERNAL_API 443 (msg:"Allow DEV to PROD internal API over TLS"; flowbits:set,allow; flow:to_server; sid:10003;)
- 此规则识别并标记从开发环境到生产内部 API 的 HTTPS/TLS 流量(端口 443)为允许状态。
tls协议匹配器专门查找 TLS 加密流量。与上一条规则类似,它设置 “allow” flowbit 以将此连接标记为允许。
# Mark HTTP connection from DEV to PROD internal API as allowed
alert http $DEV_CIDR any -> $PROD_INTERNAL_API 80 (msg:"Allow DEV to PROD internal API over HTTP"; flowbits:set,allow; flow:to_server; sid:10004;)
- 此规则识别并标记从开发环境到生产内部 API 的 HTTP 流量(端口 80)为允许状态。
http协议匹配器专门查找 HTTP 流量。这允许对内部 API 进行加密(TLS)和非加密(HTTP)访问。
# Reject any other TCP connections from DEV to PROD (Send a TCP reset so it's clear the connection was blocked by firewall and not a routing issue)
reject tcp $DEV_CIDR any -> $PROD_CIDR any (msg:"UNAUTHORIZED DEV -> PROD TCP CONNECTION ATTEMPT"; flowbits:isnotset,allow; flow:to_server; sid:10005;)
- 此规则阻止从开发环境到生产环境中未被之前规则标记为允许的任何 TCP 流量。
flowbits:isnotset,allow关键字检查此连接上是否未设置 “allow” 标志。reject动作向源端发送 TCP 重置数据包,明确反馈该连接已被主动阻止。
# Drop any other IP connections from DEV to PROD (Catch all drop rule for non TCP based protocols)
drop ip $DEV_CIDR any -> $PROD_CIDR any (msg:"UNAUTHORIZED DEV -> PROD NON-TCP CONNECTION ATTEMPT"; flowbits:isnotset,allow; flow:to_server; ip_proto: !TCP; sid:10006;)
- 这是一条兜底规则,阻止从开发环境到生产环境的任何非 TCP 流量(UDP、ICMP 等)。
ip_proto: !TCP专门匹配任何非 TCP 的 IP 协议。drop动作静默丢弃数据包。此规则确保环境之间完全隔离,仅允许特定的已授权连接。
理解 flowbits: flowbits 关键字允许规则通过在网络流上设置和检查有状态标志来相互通信。在此规则集中,flowbits 实现了一种允许列表方法,将特定连接标记为允许(flowbits:set,allow),其他所有连接均被阻止(flowbits:isnotset,allow)。有关更多信息,请参阅 Suricata 文档
。
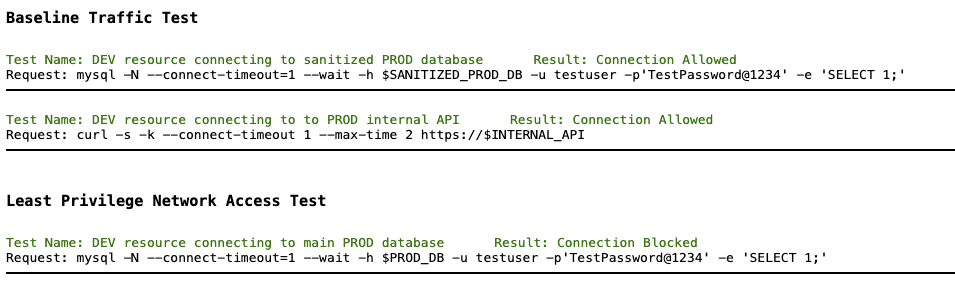
验证
- 返回 DEV 到 PROD 测试脚本并刷新页面
- 验证对主 PROD 数据库的访问现已被阻止: