NFW简介
核心组件
Rule Group(规则组)
定义:可复用的规则集合,定义如何检查流量和处理匹配的数据包
Rule Group
├── 检查条件(Inspection Criteria)
│ └── 源/目标 IP、端口、协议、域名、内容...
│
└── 处理动作(Action)
└── Pass / Drop / Alert / Reject
| 类型 | 说明 | 适用场景 |
|---|---|---|
| Stateless Rule Group | 无状态,逐包检查 | 快速过滤、黑名单 |
| Stateful Rule Group | 有状态,跟踪连接 | 深度检测、域名过滤、IPS |
特点:可复用,一个 Rule Group 可以被多个 Policy 引用
Rule Group A ──┬──► Policy 1
└──► Policy 2
Rule Group B ──┬──► Policy 1
└──► Policy 3
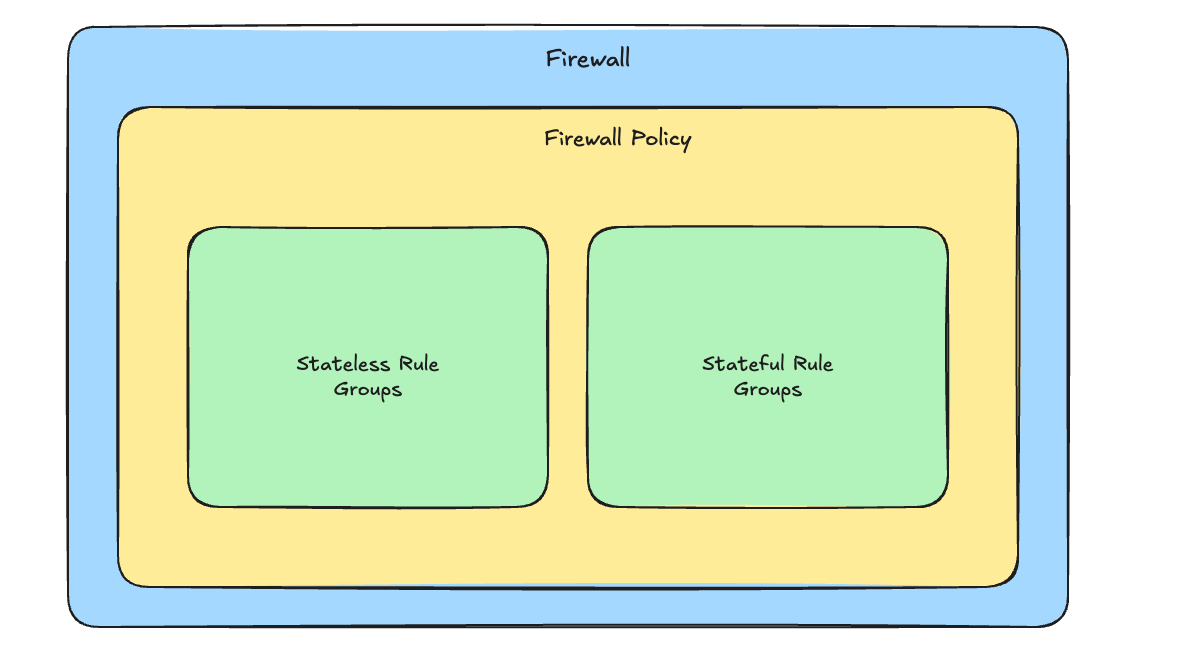
Firewall Policy(防火墙策略)
定义:组合多个 Rule Group + 策略级别的行为设置
Firewall Policy
├── Stateless Rule Groups(按优先级排序)
│ ├── Rule Group A (优先级 100)
│ └── Rule Group B (优先级 200)
│
├── Stateful Rule Groups
│ ├── Rule Group C
│ └── Rule Group D
│
└── Policy-level Settings(策略级设置)
├── Stateless Default Actions
├── Stateful Default Actions
└── Stateful Rule Order
| 设置 | 说明 |
|---|---|
| Stateless Default Action | 不匹配任何规则时的默认动作 |
| Stateful Default Action | 有状态规则的默认动作 |
| Rule Order | 规则评估顺序(Strict / Action Order) |
特点:可复用,一个 Policy 可以被多个 Firewall 使用
Firewall Policy X ──┬──► Firewall 1
└──► Firewall 2
Firewall(防火墙)
定义:将 Policy 与 VPC 关联,创建实际的防火墙实例
Firewall
├── 关联的 Firewall Policy(1 个)
├── 关联的 VPC(1 个)
├── Primary Endpoint Subnet(创建时指定)
├── Logging Configuration(日志配置)
│ ├── Flow Logs
│ ├── Alert Logs
│ └── TLS Logs
└── Other Settings
└── Delete Protection, etc.
| 配置 | 说明 |
|---|---|
| VPC | 防火墙保护的 VPC |
| Policy | 使用哪个 Firewall Policy |
| Subnet | 部署 Endpoint 的子网 |
| Logging | 日志发送到 S3/CloudWatch/Kinesis |
创建后:自动在指定子网创建 Primary Firewall Endpoint(ENI)
它们的关系:
┌─────────────────────────────────────────────────────────────┐
│ 层级关系 │
├─────────────────────────────────────────────────────────────┤
│ │
│ Rule Group (可复用) │
│ │ │
│ ▼ │
│ Firewall Policy (可复用) │
│ │ │
│ ▼ │
│ Firewall (实例) │
│ │ │
│ ├──► Primary Endpoint (创建时自动生成) │
│ └──► VPC Endpoint Association (可选,多 AZ) │
│ │
└─────────────────────────────────────────────────────────────┘
工作原理
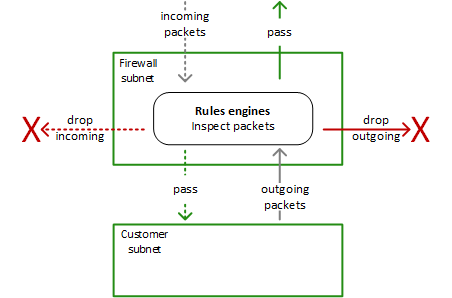
| 流程 | 说明 |
|---|---|
| 1. 流量先到 Firewall 子网 | 所有流量必须经过 NFW |
| 2. Rules Engine 检查 | 根据规则判断 Pass 或 Drop |
| 3. Pass → 放行 | 合法流量进入 Customer 子网 |
| 4. Drop → 丢弃 | 恶意/违规流量被拦截 |
它入站和出站都会检测:
| 方向 | 检查内容 |
|---|---|
| Incoming(入站) | 外部 → 内部,防入侵 |
| Outgoing(出站) | 内部 → 外部,防数据泄露、C2 通信 |